Technology Consulting for Cybersecurity in the Era of Big Data
Table of Contents
ToggleCybersecurity consulting services are crucial for protecting big data from cyberattacks, which are on the rise. Companies invest in cybersecurity consulting firms to identify overlooked vulnerabilities, implement proper security measures, and fulfill compliance requirements. These consulting solutions offer the right security solutions that improve IT security strategy, leading to customer trust and loyalty. With the proper guidance and implementation of cybersecurity initiatives, companies can protect their data, deliver a high-quality user experience, and avoid hefty fines and fees.
In January 2021, four zero-day exploits occurred at the on-premise Microsoft Exchange Servers. Attackers accessed the username and passwords of the affected users. Zero-day exploits happen when hackers identify vulnerabilities in the system before the developers. It can take days, or even years to discover the vulnerability that led to the attack.
It is estimated that around 250,000 servers were attacked. It included servers of 30,000 organizations in the US, 7,000 servers in the UK, and the servers of the European Banking Authority and the Norwegian Parliament.
The hackers installed web shell malware, which gave them administrative access to the servers. They exploited several exchange vulnerabilities in the servers of all 30,000 organizations. Such an attack is known as a supply chain attack, which gives hackers access to the data of the company’s customers.
A similar yet monetary expansive attack took place in 2020. Acer’s identity and corporate data were leaked on a public website, and the hackers gave the company a stipulated period to pay the ransom. The company was forced to pay a $50 million ransom – the largest in the history of ransomware attacks.
(Source: Springboard)
Cybersecurity in Big Data: Reality Check
It takes the security team an average of 277 days to identify and contain a data breach. Unfortunately, the duration can result in unwanted data usage that can impact the company and the customers.
In 2022, phishing attacks increased by 61%. It was observed in the third quarter of 2022 that a total of 3 million phishing attacks took place in the 3-month timeframe. Phishing attacks are the biggest threats to big data because they steal confidential information, including customer usernames, passwords, and credit card information.
By 2024, the cost of data breaches will rise from $3 trillion to $5 trillion. Without a proper incident response team in place, cyberattacks will multiply. Adequate training is now given to employees to ensure security remains top-notch. The goal is to bring down the cost of such incidents.
Read more: Are Digital Ecosystems Better or Worse for Modern Enterprise?
Role of Technology Consulting in Cybersecurity
Technology consulting services are at the forefront of the IT revolution. As a result, they play a crucial role in cybersecurity in a digital era. Cybersecurity consulting services are rising due to a massive increase in cyberattacks.
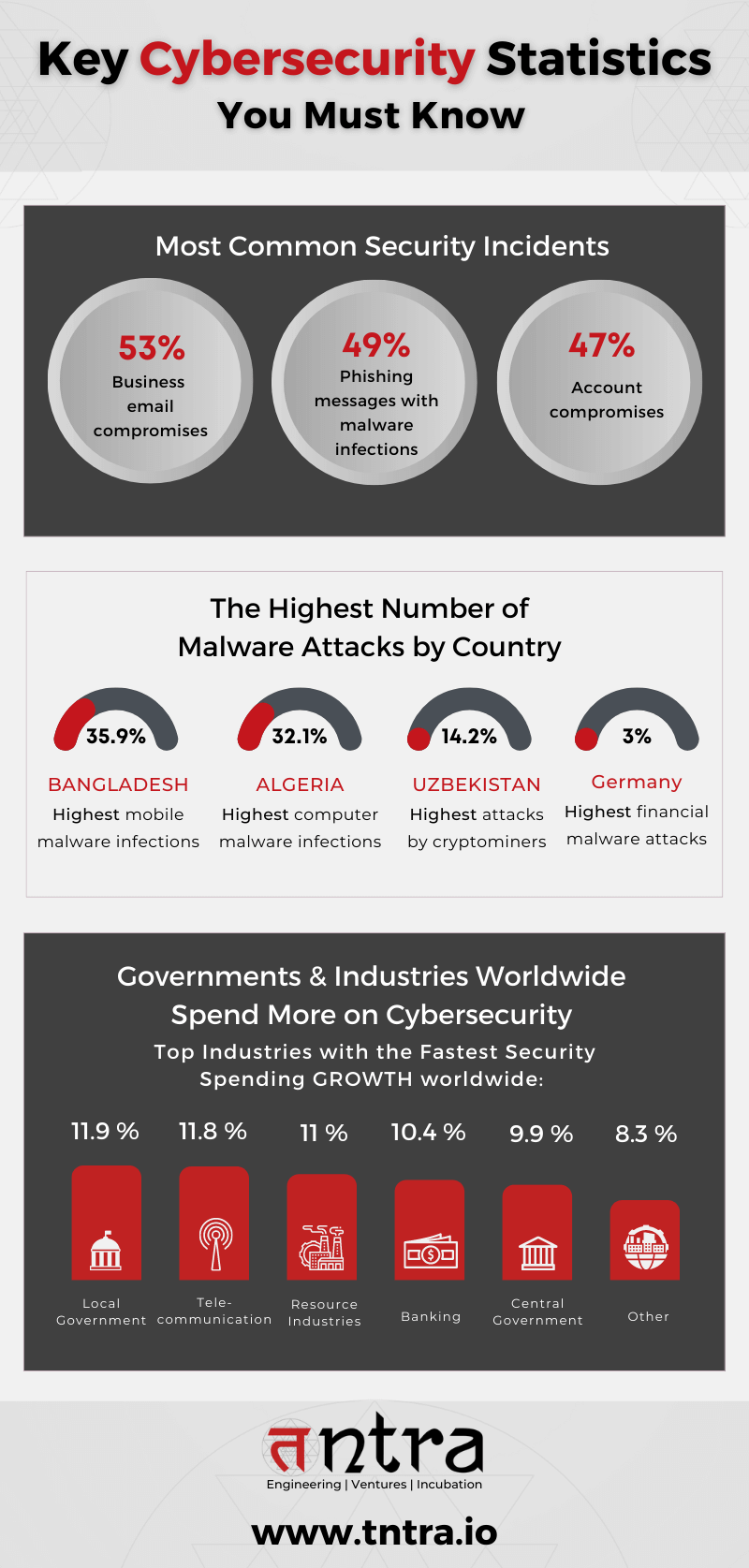
Companies are heavily investing in cybersecurity consulting firms to save themselves from hackers and cyberattacks. However, technology consulting solutions are now cybersecurity enablers for big data, mobile computing, and other data-intensive technologies.
As more and more data is generated, companies must identify how to protect it. Consumer trust is based on data protection. If sensitive data reaches the wrong hands, they lose confidence while being helpless about their lost data.
That’s when the best cybersecurity consulting providers step in. Here’s how they help an organization make the most of cybersecurity in the era of big data:
- Identify Overlooked Vulnerabilities
- Internal security teams often overlook the apparent vulnerabilities that result in cyberattacks. Security consulting services have experts who bring outside opinions and inputs, leading to a better understanding of the system. They can identify vulnerabilities and threats that go unnoticed and implement a plan of action. Besides that, consultants also bring a new perspective on the existing security measures and find anomalies in the current methods.
- Implement Security Measures
- While identifying vulnerabilities is one job, a cybersecurity consultant skills also include implementing the proper security measures. It involves creating a cybersecurity strategy and executing data protection methods, antivirus, firewalls, encryptions, and other security methods. They aim to protect data from unauthorized individuals or people outside the organization. By improving the company’s IT security strategy, consultants help gain customer trust and confidence. Companies like Tntra industry solutions provide the right security solutions that lead to customer loyalty.
- Fulfill Compliance Requirements
- Compliance is a big deal for cybersecurity in the technology consulting industry. Organizations often struggle to follow the rules and policies set in the cybersecurity space. Technology consulting for cybersecurity helps with compliance by assisting organizations in adhering to the guidelines and rules in the cybersecurity space. They can assist businesses in understanding these regulations and make sure they comply with them. A significant benefit is that technology consultants in cybersecurity ensure companies avoid the hefty fees and fines that come with ignoring the guidelines.
Discover how Tntra helped revolutionize loan management with their cutting-edge system. Check out our FinTech case study on their loan management system solution.
Conclusion
Cybersecurity is emerging as one of the most critical fields in the software product engineering services industry. Companies rely heavily on data to make insightful decisions and deliver a high-quality user experience. Cybersecurity consulting services can help companies protect their data, identify and eliminate vulnerabilities in the system, and execute a strategy that can deliver the best results from their cybersecurity initiatives.
Regarding technology consulting and software product engineering solutions for cybersecurity, Tntra technology solutions has the correct answers. Our domain experts and developers enable you to achieve complete safety from security vulnerabilities and build a secure internal system.
Contact Tntra, the expert software product engineering company.